how to hack a phone
A Media Access Control address (MAC address) is a 12-character unique identifier assigned to a specific piece of hardware such as the network adapter of your WiFi device. In simple words, a MAC address can be used to uniquely identify your Android phone on the Internet or the local network. Apr 08, 2020 To hack a phone remotely, you will need the assistance of a powerful spying tool. With the rest of the contents, we intend to emphasize the best methods to hack a phone camera. If you wish to find out How to hack an iPhone remotely & hack a Samsung phone remotely, just click to. Carter P, reader of The Unofficial Apple Weblog (TUAW), emailed in to ask crack iPhone hacker Erica Sadun to write him a MAC address spoofing application for the iPhone. In an amazing fit of.
To begin with a day till the night, we all are busy with our smartphones. We all know that the smartphones have become an important part of our life. Most importantly, we use smartphones to connect with people. But everything in this universe has it’s pro and cons as well. So, there are several advantages and several problems with smartphones which may affect our life. For example, as a parent or head of a company, we can have a fear of getting our child in wrong hands or getting cheated by our employees. In order to prevent this situation from occurring, one of the best ways is to track them and their phone. In this article, I will try to tell you almost everything about how to hack a phone.
How to Hack a Phone (Android)?
- Jan 29, 2018 Following are the easy and general steps that you have to follow while finding WiFi MAC Address on iPhone and iPad running iOS 11 or iOS 10 firmware. Step 1: Go to “Settings” and open “General.” Step 2: Tap on “About” option. Here you will find numerous information related to your device such as IMEI, serial number, device model number as well as other important information.
- Jun 08, 2019 Android Phone Hacking Features: Total Anonymity – Victim will never realized the he/she is being hack at any point of the time. Complete access to his mobile – Text Messages, File Manager (videos, images and files). Victim’s mobile could be used for variety of purposes such as a microphone, a camera, to send SMS.
A while ago, I watched a documentary on two white hat hackers, hacking about 12 students mobiles. However, their attack method was outdated compared to present one. They used two laptops, and Maltego CE Transformers to create a MiTM (Man-in-The-Middle) attack. They actually proved their point by entering some of the students mobiles, accessing their Facebook accounts, reading their emails, this was a test just to show what they could do.
The main part of their attack was the Wi-fi pineapple which costs $100. There are tons of software which are avilable for free on the internet like the raspberry pi v3 and kali Linux. In my next post, I will try to cover some basic concepts of it.
MAC Spoofing
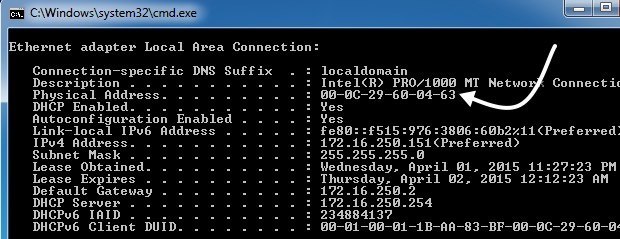
A Media Access Control address is a 12-character unique identifier assigned to the network adapter of your WiFi device. A MAC address can be used to uniquely identify the smartphone of your friend whom you want to hack the Whatsapp account. If you want to access the WhatsApp account of your friend, you need to find the MAC address of their account. Follow the below steps in order to hack your friend’s account.
First, uninstall WhatsApp from your device. Secondly, acquire the smartphone of the target(victim) that you wish to hack. The victim’s mobile phone will be essential at two variant steps throughout the hacking process. Be cautious while using the victim’s phone. Don’t take much time and try to place it back before the victim starts to locate the device. Thirdly, locate the MAC address from the target’s phone. A MAC address is a 12-character identifier.
A MAC address varies from one device to other. So, try to find the platform of the victim’s smartphone. Also, find the MAC address of your own smartphone and save it in a secure manner.
Next, spoof your MAC address similar to the victim’s MAC address. by doing this, the MAC address allow your mobile device to disguise as victim’s device. Also, there is an advantage of letting you persuade WhatsApp that you are logging into your own account. But, truly you are trying to log in into the victim’s WhatsApp account. Next, install various spoofing applications depending on the victim’s smartphone. For android device, go for terminal emulator and busy box. For IOS device, go for MacDaddy X or Wi-fi Spoof.
How to Hack a Phone using Terminal Emulator
While using terminal, type “ip link show” and it will show a list of interfaces. after that, identify the one which has your MAC address.
In the terminal emulator, enter “ip link set eth0 address XX:XX:XX:XX:XX:XX” and “ip link set eth0 broadcast XX:XX:XX:XX:XX:XX”, where eth0 is the interface you identified and XX:XX:XX:XX:XX:XX is your target’s MAC address. Next, reinstall and configure WhatsApp in your smartphone. After doing this, you can access the victim’s account. So, start this by adding the phone number of the victim’s account while setting up the account. This allows you to receive and send messages from the victim’s account.
During the configuration process, the confirmation code will be sent to victim’s phone number. Access the victim’s phone for the last time to acquire that verification code. Enter that code in your phone and you are good to go. Next, change your MAC address as quick as possible after successfully accessing the victim’s phone.
How to Hack a Phone using Spyware?
According to the current market trend, there are many companies that are promoting spyware applications and people are willing to pay for it. But before doing such thing, choose only genuine companies which are trustworthy. According to me, MySpy is one of the most trustworthy spying application available on play store. You will have to download and install the mySpy app onto the victim’s phone on which you want to access and monitor the WhatsApp messages. The spy apps that you use are very much essential and intended for the employees, parents, government officials in order to access or monitor the activities of subordinates, children and other . Here are some steps on “how to hack a phone using MySpy” application.
First of all, make sure that the victim gives permission to access and monitor their mobile. After that, install MySpy on your phone as well as on victim’s phone. Next, follow the instructions carefully so as to install the app and make sure that you configure all your settings properly. Now it’s time to start our hacking process. Now, you can receive and send messages on the victim’s account. Finally, you’ve have hacked the victim’s account. If you’ve any other great ideas, comment down below and don’t forget to follow us on Instagram.
